3 Tips to Arm Yourself From Phishing Scams

Phishing is one of the most dangerous and compromising scams on the Internet. “Phishing” refers to an attempt to acquire sensitive information such as your login credentials or passwords by pretending to be a trustworthy source such as your bank or email provider. The anatomy of a phishing email is simple: a service you may or may not subscribe to appears to send you an email and asks you to login to your account. They even provide you with a handy link to click.
Unknowing to you, the phishers have created a website that looks identical to the service you are used to logging into (for example, Chase Bank). Since this is a fake website, the phishers can not host it on https://www.chase.com. Instead, they create a website with a similar URL. It may be something like http://chase-bank.blanco.cn/login. This is a fake URL, but most people will not hesitate to click the link because it says the name of the service in it.
And that’s how it all begins…
You click the link and it brings you to a website that looks identical to Chase Bank’s website. You enter your information into a login form, and the phishers gain access to your account.
Anyone can be a victim of a phishing scam
The truth is, we all lead busy lives and a phishing attempt can come in an email that looks and reads like a legitimate source. For example, if you’re the CMO of an organization and you get an email that appears to be from your accounting department requesting that you approve the new marketing expense, you may instinctively click the link because it seems to be coming from a familiar source. You enter your email and password to log onto the page only to learn after-the-fact that your organization has now been hacked. Don’t let that happen to you.
How to pick out a phishing email:
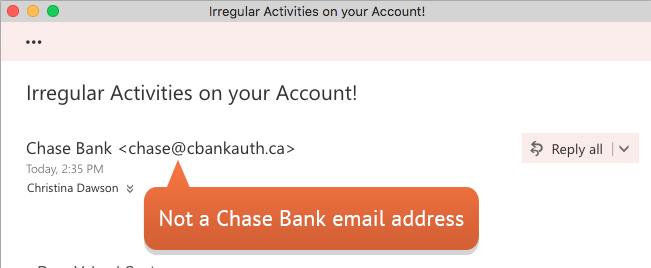
- What email address did it come from? Does it look bogus? If so, it probably is. Emails from services you use regularly such as your bank, Netflix, PayPal, etc. come from the same domain every time. Double check the email address for any irregularities.
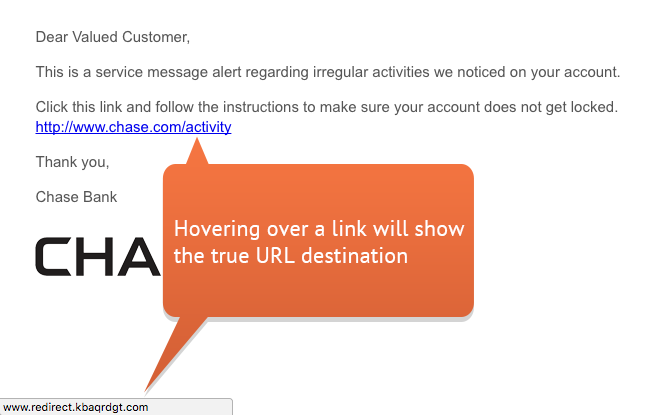
- Check the true destination of an URL before clicking it. Hovering over a link with your mouse will show you the entire URL. Does the link go to a website you recognize? Be sure to look carefully so you don’t fall for the Chase Bank scheme mentioned earlier. Another way to know if a website is legitimate is if they use Secure Sockets Layer (SSL), which creates an encrypted connection between your web server and your visitors’ web server. You know a website is using SSL if its address begins with https:// (notice the “s”) rather than http://
- Look for misspellings. Many phishing emails have obvious typos, grammar issues, improper capitalizations, and irregular exclamation points. Legitimate services double-check their emails for proper spelling and phrasing before sending them out. You may even notice the email is addressed to “Sir/Madam” or “Dear Customer”. Your bank, Facebook, and PayPal accounts know your name. Even with this information, scammers are becoming more sophisticated and targeting people with well-written emails that include their names
Still unsure if it’s a phishing scam?
Take the cautious approach. Don’t click any links in the email or respond to the email. Instead, visit the website the email claims to be from on your own. If the email claims it’s from Facebook, open your web browser and type in www.facebook.com in the address bar and log in to your account to change your password from there. You know you’re on the real Facebook site because you visited it yourself and not from a link in a suspicious email.
Now that you’ve armed yourself with these shields against phishing scams, you are set for the next time a ‘phisher’ tries to drop a line. (See what we did there?)
Download our Cyber Security eBook for more ways to arm yourself against cyber criminals.
- How Active Directory for Windows can be a lifesaver - January 14, 2018
- Keep your identity safe with Two-Factor Authentication - July 11, 2017
- 3 Steps to Prevent Malware Attacks like WannaCry - May 17, 2017